CoWSwap Hack: Urgent Security Alert as Frontend Attack Targets User Wallets
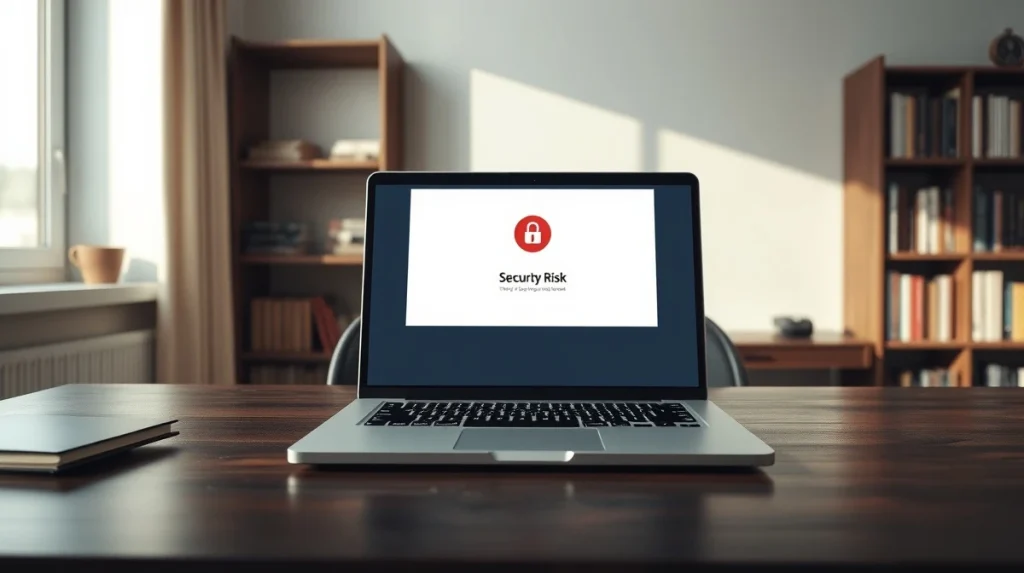
A major security breach has hit the decentralized finance (DeFi) space. On April 14, 2026, the frontend of the popular decentralized exchange CoWSwap was compromised in a targeted attack. Security firms and blockchain analysts quickly flagged the site as malicious. They urged all users to immediately revoke wallet permissions granted to the platform. This incident highlights persistent vulnerabilities in the user-facing layers of DeFi applications.
CoWSwap Frontend Attack: What Happened
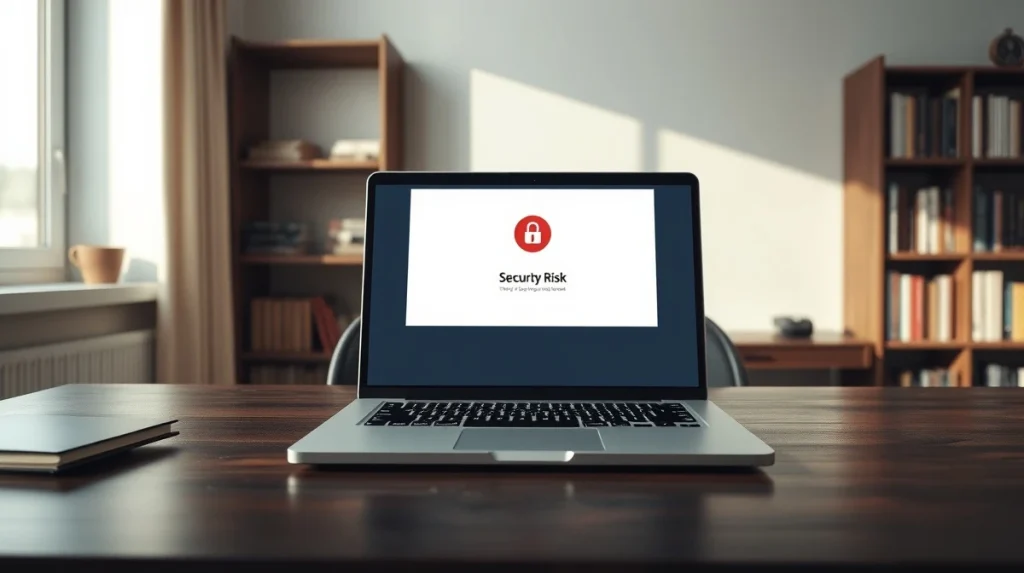
The attack did not target the underlying CoW Protocol smart contracts, which remained secure. Instead, hackers compromised the website’s frontend—the interface users interact with at swap.cow.fi. According to blockchain security firm BlockSec, which first raised the public alarm, the attackers injected malicious code. This code could have manipulated transaction details before users signed them with their wallets. The goal was likely to drain funds by tricking users into approving harmful transactions. The CoW Protocol team confirmed the incident on their official social media channels. They advised users to avoid the site until a full investigation was complete.
Also read: SUI Price Breakout: Bulls Target a Fresh Upward Trend Above $1.12 Resistance
Immediate User Actions Required
The primary risk for users stems from pre-approved token allowances. When interacting with any DeFi application, users often grant permission for a smart contract to spend specific tokens from their wallet. If the frontend is malicious, it can request excessive or dangerous allowances.
Security experts recommend these immediate steps:
Also read: Solana Active Addresses Fall Sharply While Bullish Sentiment Surges to January Highs
- Revoke all token approvals granted to the CoWSwap contract. Users can do this through wallet management tools like Revoke.cash or Etherscan’s Token Approval checker.
- Avoid connecting your wallet to the CoWSwap website until the team confirms the frontend is clean.
- Consider using a brand-new wallet for future DeFi interactions if you interacted with the site during the attack window.
- Monitor your wallet transactions for any unauthorized activity.
Data from DeFi safety platform RugDoc shows that frontend exploits have become a common attack vector. They accounted for nearly 30% of all major DeFi security incidents in the first quarter of 2026.
The Frontend Vulnerability Problem
This attack underscores a critical weakness in DeFi security models. While billions are spent auditing immutable smart contract code, the traditional web infrastructure hosting the user interface is often a softer target. “The frontend is the most centralized part of a decentralized exchange,” noted a report from CertiK, another security auditor. “It’s a single point of failure that can undermine all other security measures.” The CoWSwap team likely relied on a third-party domain or hosting provider that was compromised. This suggests that even projects with solid smart contract security can fall victim to conventional web attacks like DNS hijacking or server breaches.
Broader Impact on DeFi and User Trust
Incidents like this erode user confidence. They create friction and fear at the exact point of interaction—the website. For an industry built on self-custody and personal responsibility, convincing users to click ‘Approve’ is fundamental. When the interface itself cannot be trusted, participation drops. Trading volume on CoWSwap fell to near zero following the alert, according to Dune Analytics dashboards tracking the protocol. This has a direct financial impact on liquidity providers and the protocol’s fee revenue. The implication is clear: security must involve the entire user journey, not just the blockchain layer.
How This Compares to Other DeFi Hacks
This event differs from major smart contract exploits like the 2022 Wormhole bridge hack or the 2023 Euler Finance attack. Those involved flaws in the protocol logic itself. The CoWSwap incident is more akin to a phishing attack, using a trusted domain to deceive users. It shares similarities with the 2024 attack on Curve Finance’s frontend, where a domain name system (DNS) compromise led to a $570,000 loss. The table below contrasts the attack vectors.
| Incident | Year | Primary Vector | Estimated Loss |
|---|---|---|---|
| Curve Finance Frontend | 2024 | DNS Hijacking | $570,000 |
| CoWSwap Frontend | 2026 | Frontend Code Injection | Under Investigation |
| Wormhole Bridge | 2022 | Smart Contract Exploit | $325 million |
Industry watchers note that frontend attacks typically result in smaller direct losses. Their real damage is to trust and usability. What this means for investors is increased scrutiny on a project’s operational security, not just its code audits.
Response and Mitigation Strategies
The CoW Protocol team took the standard corrective actions. They took the frontend offline, began forensic analysis, and communicated with users. To prevent future occurrences, projects are adopting new strategies. Some recommend using decentralized frontends hosted on networks like IPFS or Arweave. Others advocate for wallet-level security features. For example, the Rabby wallet includes a transaction simulation that shows users exactly what will happen before they sign. This could have flagged malicious requests from a compromised frontend. The long-term solution may involve a shift in how users access DeFi. Browser extensions and application interfaces that verify the integrity of a site’s code before connecting are in development.
Conclusion
The CoWSwap hack is a stark reminder that security in decentralized finance is multifaceted. A strong smart contract audit is not enough. Users must treat the web interfaces of DeFi apps with the same caution as any other website. They should regularly review and revoke token allowances. For developers, securing the frontend is now as critical as securing the protocol. As DeFi evolves, protecting the gateway between users and the blockchain will remain a top priority. This incident will likely accelerate the adoption of more resilient access methods and better user education.
FAQs
Q1: Was my money stolen if I only visited the CoWSwap site?
Not necessarily. The attack required users to sign a malicious transaction. Simply visiting the site with a wallet connected, but not approving any transactions, likely posed minimal risk. However, revoking permissions is still advised.
Q2: How do I revoke token approvals for CoWSwap?
Use a permission management tool. Go to a site like Revoke.cash, connect your wallet, and search for approvals related to the CoWSwap contract address (0x9008D19f58AAbD9eD0D60971565AA8510560ab41 on mainnet). Then revoke them.
Q3: Is the CoW Protocol itself safe to use now?
The underlying CoW Protocol smart contracts were not breached. Once the team redeploys a verified, clean frontend, the protocol itself should be safe to use. Always wait for an official all-clear from the team.
Q4: What are the signs of a compromised DeFi frontend?
Unusual transaction requests, mismatched contract addresses in your wallet pop-up, or website URLs that don’t exactly match the official domain. Wallet simulation tools that show unexpected token movements are a major red flag.
Q5: Can this happen to other decentralized exchanges?
Yes. Any DeFi application that uses a standard web frontend is potentially vulnerable to similar attacks. The risk is not unique to CoWSwap. It’s a systemic challenge for the industry.