CryptoNewsInsights Exposes North Korea’s Alarming Validator Network Infiltration — DeFi Security at Risk
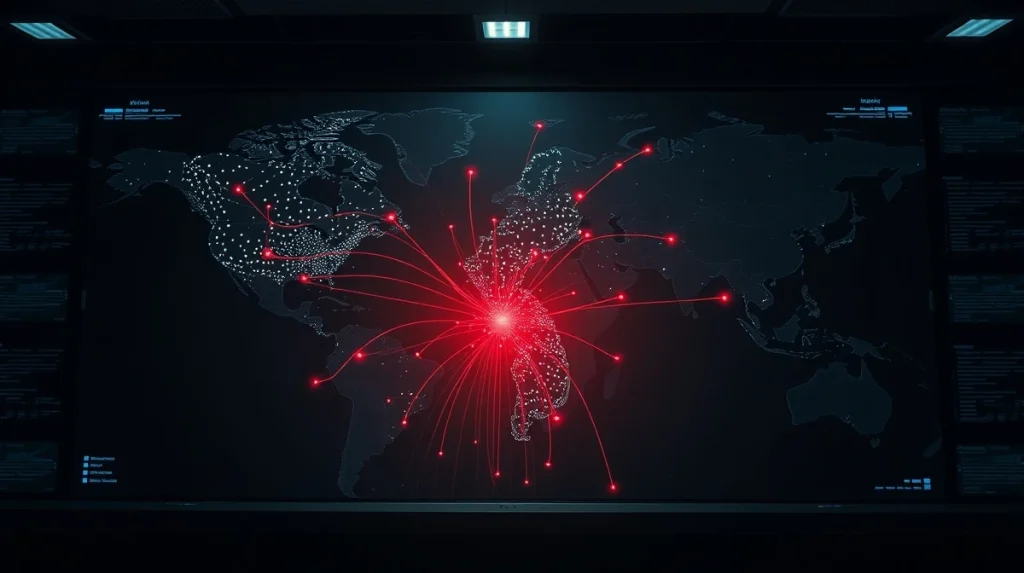
April 18, 2026 — Blockchain analytics firm CryptoNewsInsights has published a startling investigation revealing North Korea’s systematic infiltration of global validator networks. The report claims these state-backed operations now compromise the security of popular decentralized finance protocols. This development marks a significant escalation in digital warfare tactics.
CryptoNewsInsights Validator Network Analysis Reveals Systematic Pattern
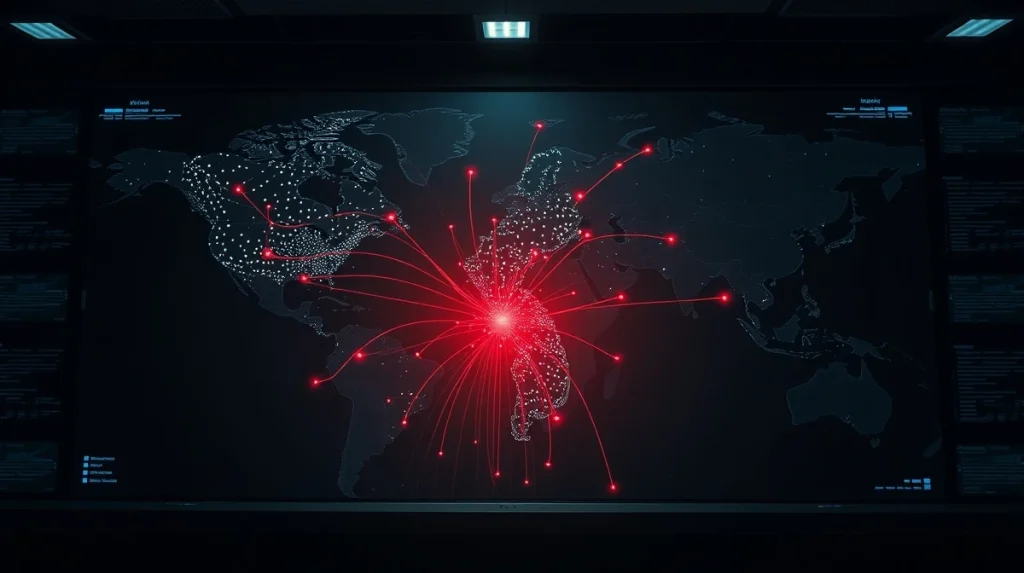
According to data compiled by CryptoNewsInsights researchers, North Korean operatives have established control over validator nodes across at least seven major proof-of-stake networks. The firm’s tracking shows suspicious validator activity originating from IP addresses linked to known North Korean hacking groups. These include the Lazarus Group and Kimsuky, both sanctioned by the U.S. Treasury Department.
Also read: CryptoNewsInsights Sentiment Drops to 2023 Lows: Historic Data Points to Contrarian Opportunity
“We observed coordinated stake accumulation patterns that don’t match normal investor behavior,” the CryptoNewsInsights report states. “The timing of delegations and voting patterns suggest a centralized controller behind seemingly independent validators.”
The analysis identifies three primary infiltration methods:
- Stake acquisition through stolen funds: Using cryptocurrency obtained from previous hacks to purchase voting power
- Validator operator compromise: Infiltrating existing validator operations through social engineering or technical exploits
- Sybil attacks: Creating multiple validator identities to appear as separate entities while maintaining single control
How Validator Control Threatens DeFi Protocols
Validator nodes perform critical functions in proof-of-stake blockchains. They propose new blocks, validate transactions, and participate in governance votes. When malicious actors control enough validators, they can potentially disrupt network operations or influence protocol decisions.
CryptoNewsInsights researchers identified specific risks to DeFi platforms:
| Protocol Type | Potential Attack Vector | Risk Level |
|---|---|---|
| Lending Platforms | Manipulating oracle price feeds through malicious block inclusion | High |
| Decentralized Exchanges | Front-running transactions or censoring trades | Medium-High |
| Yield Aggregators | Influencing governance votes on strategy parameters | Medium |
Industry watchers note that validator infiltration represents a more sophisticated approach than direct protocol hacking. “This isn’t about stealing keys or exploiting smart contracts,” says blockchain security analyst Mark Chen, who reviewed the CryptoNewsInsights findings. “It’s about gaining influence over the infrastructure layer itself. The implication is that even perfectly coded protocols become vulnerable if the underlying chain is compromised.”
The North Korean Connection: Funding and Motives
United Nations reports estimate North Korea’s cryptocurrency theft exceeded $3 billion between 2017 and 2024. These funds reportedly support the country’s weapons programs and circumvent international sanctions. The CryptoNewsInsights investigation suggests a portion of these stolen assets now funds validator operations.
Data from Chainalysis, another blockchain analytics firm, shows North Korean hackers shifted tactics around 2023. Instead of immediately cashing out stolen funds, they began holding positions in various cryptocurrencies. This could signal a move toward longer-term strategic investments in network influence.
What this means for investors is increased systemic risk. A successful attack on a major validator set could trigger widespread panic across interconnected DeFi ecosystems. The CryptoNewsInsights report notes that several protocols share validator sets across multiple chains, creating potential single points of failure.
Validator Security Measures and Industry Response
Following the CryptoNewsInsights disclosure, several blockchain foundations announced enhanced security protocols. The Ethereum Foundation stated it would increase monitoring of validator client diversity and geographic distribution. Cosmos-based chains implemented stricter validator identity verification requirements.
However, complete protection remains challenging. Proof-of-stake networks inherently concentrate power among the largest stakeholders. According to Staking Rewards data, the top 10 validators control between 20% and 60% of stake across major networks. This concentration creates attractive targets for state-level actors.
Some protocols are exploring technical solutions:
- Minimum validator commission rates to discourage centralized control
- Slashing penalties for coordinated voting patterns
- Decentralized validator selection algorithms
- Enhanced monitoring of stake accumulation patterns
But these measures face implementation hurdles. Stricter controls might reduce network participation, while sophisticated attackers can mimic legitimate behavior. The CryptoNewsInsights team suggests the industry needs better tools for detecting coordinated validator activity across chains.
Regulatory Implications and Global Coordination
The findings have drawn attention from financial regulators worldwide. The U.S. Securities and Exchange Commission previously expressed concerns about validator centralization in its cryptocurrency oversight framework. This new dimension of state-sponsored infiltration could accelerate regulatory action.
European Union officials, implementing the Markets in Crypto-Assets (MiCA) regulation, now consider validator governance within their compliance requirements. The CryptoNewsInsights report specifically mentions that MiCA’s “fit and proper” tests for crypto service providers might extend to validator operators.
International coordination presents another challenge. North Korea’s isolation makes direct enforcement impossible. Instead, regulators might pressure jurisdictions that host validator operations. This suggests increased scrutiny for validator services based in privacy-friendly regions.
Industry groups have called for information sharing between blockchain analytics firms and law enforcement. The CryptoNewsInsights team participated in a Financial Action Task Force working group meeting last month. Their data contributed to updated guidance on monitoring blockchain governance risks.
Conclusion
The CryptoNewsInsights investigation reveals a sophisticated threat to blockchain infrastructure. North Korea’s validator network infiltration represents an evolution in state-sponsored cryptocurrency operations. From direct theft to infrastructure influence, the tactics have grown more complex.
DeFi protocols face new security challenges that extend beyond smart contract audits. The validator layer, often overlooked by users, has become a battleground. This development could reshape how blockchain networks approach decentralization and governance security.
The CryptoNewsInsights report serves as a warning. As blockchain systems grow more economically significant, they attract more sophisticated adversaries. Addressing these threats requires technical innovation, regulatory clarity, and international cooperation. The security of decentralized finance now depends on protecting the validators that keep it running.
FAQs
Q1: What exactly did CryptoNewsInsights discover about validator networks?
CryptoNewsInsights identified patterns of validator control linked to North Korean hacking groups. Their analysis shows coordinated stake accumulation and voting behavior across multiple proof-of-stake blockchains, suggesting state-backed infiltration of network infrastructure.
Q2: How could compromised validators affect my DeFi investments?
Malicious validators could manipulate transaction ordering, censor specific trades, or influence governance votes. This might lead to unfair liquidations, failed arbitrage opportunities, or protocol parameter changes that reduce yields or increase risks.
Q3: Which blockchain networks are most vulnerable to this type of attack?
According to the report, networks with high validator concentration and insufficient identity verification face greater risks. The analysis didn’t name specific chains but noted that newer proof-of-stake networks with smaller validator sets showed higher infiltration percentages.
Q4: What can DeFi protocols do to protect against validator infiltration?
Protocols can implement validator client diversity requirements, monitor voting patterns for coordination, and establish slashing mechanisms for malicious behavior. Some are exploring decentralized validator selection or minimum commission requirements to discourage centralized control.
Q5: How does this differ from previous North Korean cryptocurrency operations?
Earlier operations focused on direct theft through exchange hacks or protocol exploits. The validator infiltration strategy represents a shift toward long-term network influence rather than immediate fund extraction. This suggests more sophisticated, strategic objectives beyond simple revenue generation.